Compliance verification for Kubernetes deployments is fundamental to deployment security. This blog explains how to verify and enforce Kubernetes compliance with OpsMx Autopilot. Dynamic Admission Control mechanisms of Kubernetes provide the right framework to achieve compliance.
Admission Control in Kubernetes
Admission control mechanism is an important construct that is going into beta in next release of Kubernetes. Read more about here. https://unofficial-kubernetes.readthedocs.io/en/latest/admin/admission-controllers
Compliance Verification need the following three pieces of the puzzle:
- Admission Control Plug-in
- Admission Webhooks
- Admission Webhooks Server
What is an Admission Control Plug-in? An admission control plug-in is a piece of code that intercepts requests to the Kubernetes API server prior to persistence of the object, but after the request is authenticated and authorized. The plug-in code is in the API server process and must be compiled into the binary in order to be used at this time”. Read more about Admission Controllers here: https://kubernetes.io/docs/reference/access-authn-authz/admission-controller
What are Admission Webhooks? Admission webhooks are HTTP callbacks that receive admission requests and do something with them.
What is an admission webhook server? Admission webhook server handles the requests sent by the apiservers, and sends back its decision.
Compliance Verification
Compliance Verification needs
- Admission Control Plug-in. To Turn-on and Off please refer https://kubernetes.io/docs/reference/access-authn-authz/admission-controllers/#why-do-i-need-them
- Admission Webhook Server – OpsMx Autopilot
OpsMx Autopilot as an Admission Webhook Server
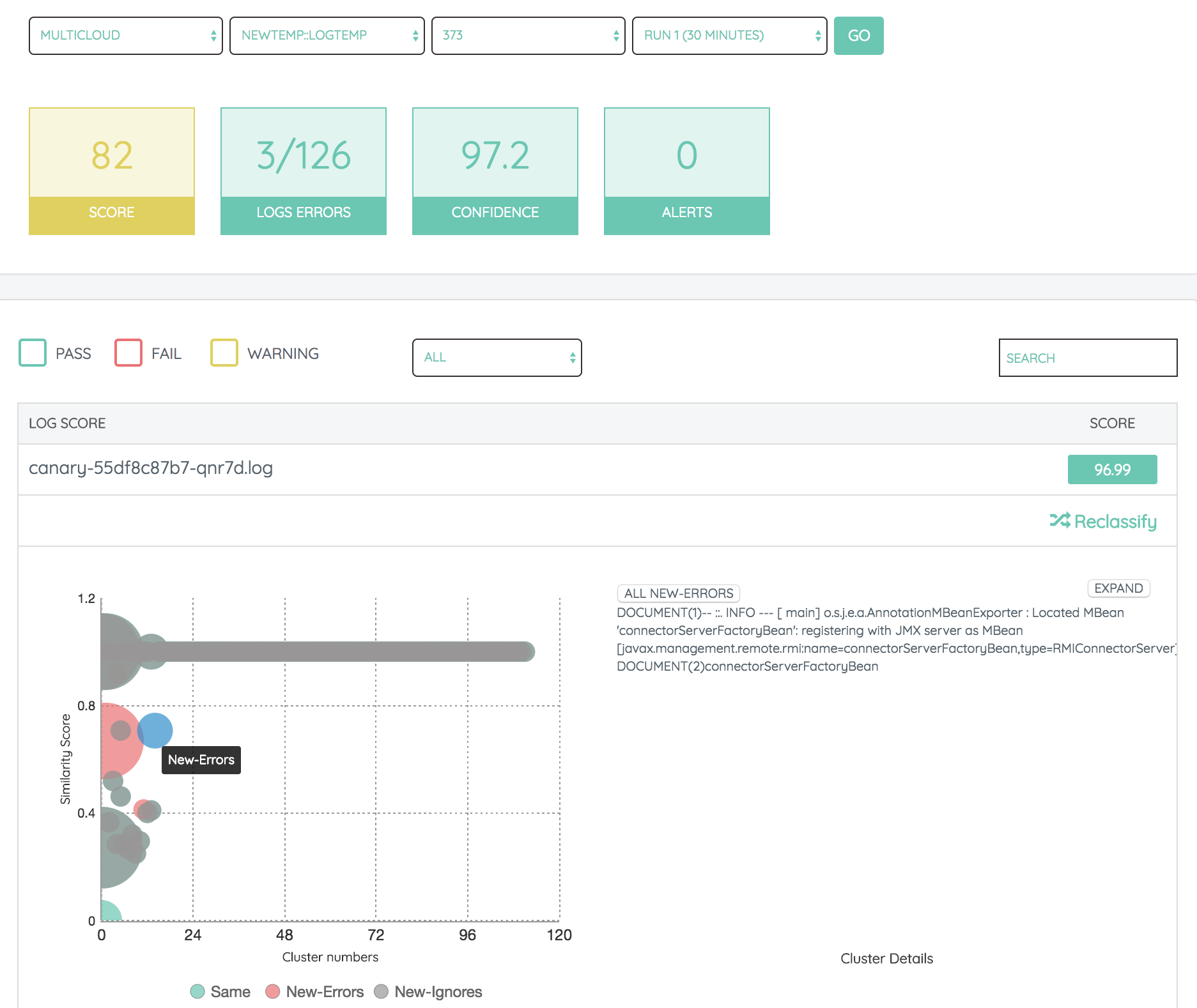
OpsMx Autopilot is an admission webhook server. OpsMx Autopilot collects and analyses Logs, Metrics, Events and data from other sources to ensure risk is being reduced and compliance is being enforced.
-
Compliance Verification with Logs using supervised and un-supervised machine learning
Autpilot provides a flexible Rules Engine for your compliance needs and it also leverages both un-supervised and supervised machine-learning to asses performance, security and compliance at Speed and Scale.
If this sounds interesting/ useful or if you would like to see a working demo of compliance verification for Kubernetes deployments, please send us an email at customer@opsmx.com

0 Comments