
In the ever-evolving digital landscape, the security of software supply chains has become a pivotal concern for organizations globally. With 61% of businesses impacted by supply chain threats last year, the urgency for robust cybersecurity frameworks is undeniable. At the center of this security endeavor stands the National Institute of Standards and Technology’s (NIST) 800-53 standard, offering an exhaustive framework to fortify cybersecurity measures in Continuous Integration and Continuous Deployment (CI/CD) processes.
NIST 800-53: A Comprehensive Cybersecurity Framework
NIST 800-53 presents itself as a comprehensive set of guidelines designed to enhance the resilience of information systems against cybersecurity threats. With over 1100 controls across 20 families, NIST 800-53 is tailored for the complex nature of modern information security. In the CI/CD context, integrating NIST 800-53 controls is crucial, embedding them into every stage of the software development and deployment process. This integration ensures comprehensive security coverage from initial code development to final deployment.
Securing the 'Last Mile' in Software Delivery
The post-build stages of the software lifecycle often termed the ‘last mile’ in software delivery, are fraught with vulnerabilities. Historical breaches like the SolarWinds incident underscore the significant risks of neglecting robust security practices in these stages. Implementing NIST 800-53 controls in the CI/CD process is about shifting from a reactive to a proactive security stance. While the ‘Shift Left’ methodology has been instrumental in incorporating security early in the development process, NIST 800-53 extends this focus to every step, right up to the release into the production environment, narrowing the window for potential attacks and fortifying the entire software delivery process.
Key NIST Controls for CI/CD Pipelines
Eight control families within NIST 800-53 are particularly relevant to software delivery and deployment:
- Access Control (AC): Ensures only authorized personnel interact with the system during critical stages.
- Audit and Accountability (AU): Captures a comprehensive record of the end-to-end process.
- System Integrity (SI): Verifies integrity of software artifacts and configurations.
- Configuration Management (CM): Maintains integrity of the deployment destination.
- Identity and Authentication (IA): Secures interactions within the software delivery process.
- System and Communications Protection (SC): Safeguards data transmission within and between systems.
- System and Services Acquisition (SA): Assures quality of systems and services integrated into the software delivery.
- Assessment and Authorization (CA): Validates security compliance of system operations.
By embedding these controls into CI/CD pipelines, organizations can achieve a robust security posture, effectively guarding against cyber threats at every phase of software delivery.
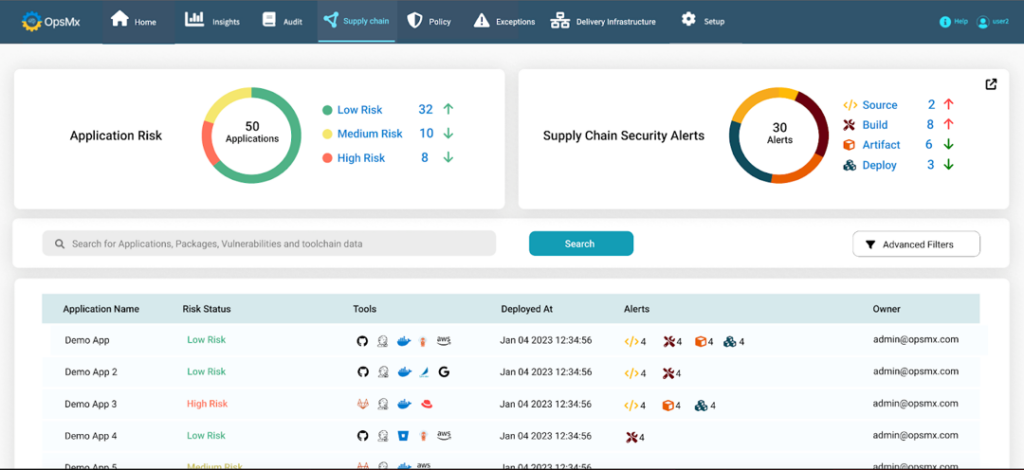
Streamlining Compliance with OpsMx Solutions
Addressing the complexities of implementing NIST 800-53 in CI/CD processes, OpsMx offers a turnkey solution. Deploy Shield and SecureCD provide a comprehensive policy framework, automated enforcement, broad tool integrations, and automated compliance audits, simplifying the task of translating NIST 800-53 controls into actionable policies. This approach not only accelerates compliance but also ensures alignment with various regulatory frameworks in a unified manner.
Leveraging NIST 800- 53 is a foundational best practice for organizations looking to bolster their software supply chain security. As software supply chain attacks rise, aligning delivery and deployment practices with NIST 800-53 is a proactive cybersecurity strategy.
For a deeper understanding and practical strategies to secure your software delivery and deployment processes, download our comprehensive whitepaper here


0 Comments