This guide explains how to configure Spinnaker v1.16.1 to trigger Spinnaker pipelines based on commits to a GitHub repository and inject the changed GitHub files as artifacts into a pipeline.
1. Prerequisites for configuring/ triggering Spinnaker pipelines through GitHub using Git push
- A GitHub repository either under your user or in an organization user’s account that you have permission to publish commits to.
- A Running Spinnaker v1.16.1
1.1. A GitHub repository either under your user or in an organization user’s account that you have permission to publish commits to.
Prepare a GitHub repository with a sample source code to build and it must contain some source code to build artifact.
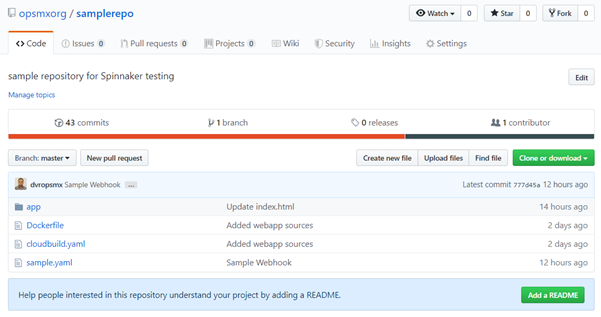
Prepare a GitHub repository
1.2. A Running Spinnaker (v1.16.1)
1. Configure GitHub Webhook :
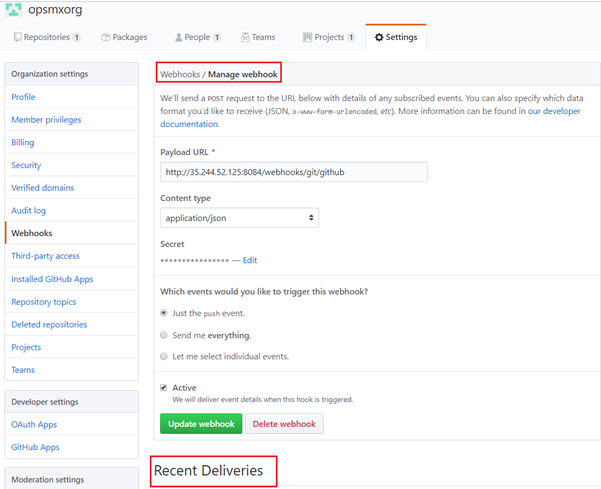
Under the GitHub repository, navigate to Settings -> Webhooks -> Add Webhook. Insert the following values in the form shown below:
Payload URL:
The Payload URL should be $ENDPOINT/webhooks/git/github
We need Spinnaker’s API running on an endpoint that is publicly reachable. This is required to allow GitHub’s webhooks to reach Spinnaker.
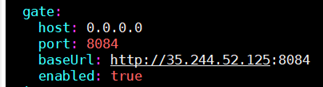
If you’re unsure of what your Spinnaker API endpoint is, check the value of
services.gate.baseUrl in ~/.hal/$DEPLOYMENT/staging/spinnaker.yml.
The value of $DEPLOYMENT is typically the default value.
Allow access to Spinnaker API endpoint
Content type:
The value should be ‘application/json’
Secret:
The value is up to you and must be provided to any GitHub webhooks triggers that you configure within Spinnaker. It’s used to ensure that only GitHub can trigger your pipelines.
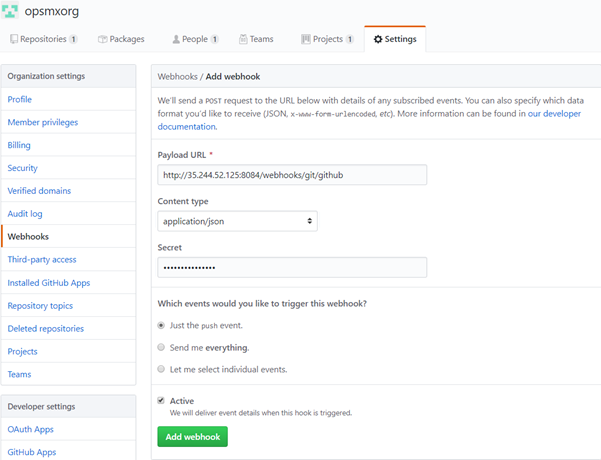
Insert the Secret credential values for GitHub Webhooks configured in Spinnaker
2. Configure a GitHub Artifact Account in Spinnaker
Spinnaker can be configured to listen to changes to a repository in GitHub. These steps show you how to configure a GitHub artifact account so that Spinnaker can download files from GitHub.
3.1. Downloading Credentials
Start by generating an access token for GitHub. The token requires the repo scope.
Here Create an access token for GitHub by following the below link:
https://help.github.com/en/articles/creating-a-personal-access-token-for-the-command-line
Generate an Access token for your GitHub account and downloaded credentials are saved in ‘git_token_file’.
TOKEN_FILE=/home/opsmxuser/dvrs/git_token_file
3.2. Editing Artifact Settings in Spinnaker Config
Enable GitHub artifact support and add an artifact account:
TOKEN_FILE=/home/opsmxuser/dvrs/git_token_file
ARTIFACT_ACCOUNT_NAME=dvr-github-artifact-account
$ hal config features edit --artifacts true
$ hal config artifact github enable
$ hal config artifact github account add $ARTIFACT_ACCOUNT_NAME --token-file $TOKEN_FILE
$ hal deploy apply
Configure Spinnaker Pipeline Trigger : Configure Spinnaker pipeline to be triggered by a GitHub commit
4.1. Configuration Stage in Spinnaker
Create a new pipeline that we want to be triggered on changes to GitHub artifacts.
- In the Spinnaker Pipeline configuration, click the Configuration stage on the far left of the pipeline diagram.
- Click on Add Artifact under the Expected Artifacts section.
- Select an artifact account that was added earlier (3.2) from the Account drop-down list and enter the File Path field.
- Note down the ‘Display name’ which is auto-generated and pass this as a value for ‘Artifact Constraints’ for Automated Triggers configuration.
Configure Expected Artifacts in Spinnaker
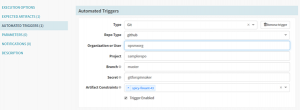
- Click Automated Triggers. In the Type field, select Git.
- In the Repo Type field, select GitHub.
- In the Organization or User field, enter the organization value of your Git repository.
- In the Project field, enter the GitHub repository name.
- Specify the appropriate branch details for the Branch.
- Provide the Secret value that was entered during GitHub Webhook configuration at Section #2.
- Select the Display name for Artifact Constraints which was generated in the Expected Artifacts section.
Configure Automated Triggers in Spinnaker
4.2. Google Cloud Build Stage
It would be very useful to be able to trigger a Google Cloud Build directly from Spinnaker. This would allow running arbitrary scripts without having to set up another service like Jenkins. The user would be providing a cloudbuild.yaml file (Cloud Build build configuration file). Spinnaker then would use its GCP service account to trigger a Google Cloud Build.
Refer to the below link for more details on the build config file.
https://cloud.google.com/cloud-build/docs/build-config
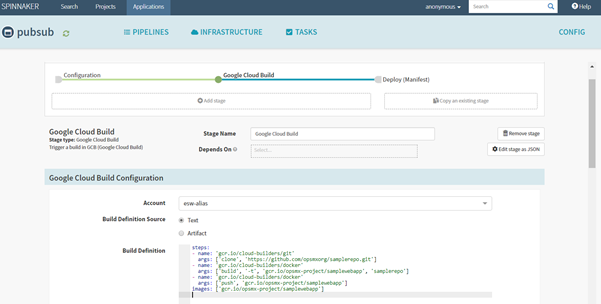
Add a Cloud Build build configuration file in Spinnaker
4.3. Deploy Kubernetes Manifests
Select the Deploy (Manifest) stage(to ‘Depends On’ Google Cloud Build stage) by specifying the manifests statistically.
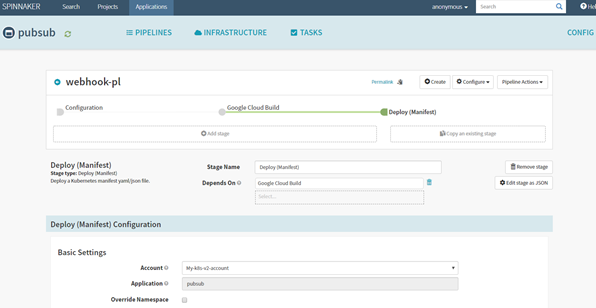
Set the Deploy (Manifest) stage depend on the Google Cloud Build stage in Spinnaker
Add manifest configuration to pull the web app image (gcr.io/opsmx-project/samplewebapp) from Google Container Registry(GCR) and deploy it on configured Kubernetes cluster(My-k8s-v2-account).
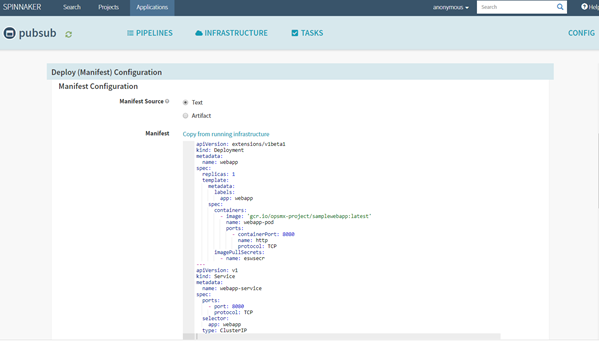
Add Kubernetes manifest configuration in Spinnaker to pull the web app image
-
-
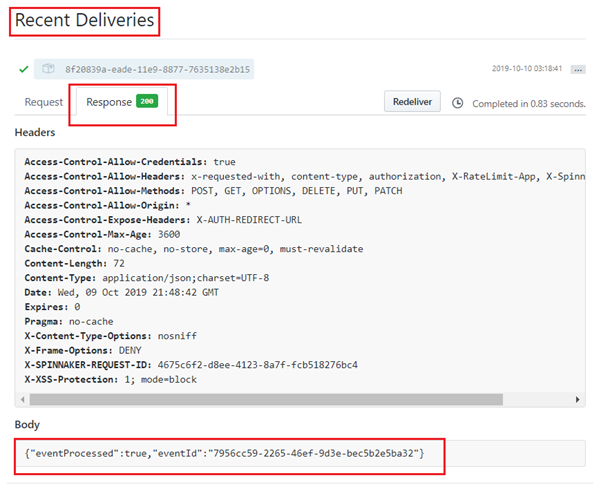
- VerificationMake a change into the repository, ex: https://github.com/opsmxorg/samplerepo.git for specified Filepath (example: sample.yaml) and ensure Spinnaker’s pipeline is auto-triggered. This can also be verified under Manage Webhook -> Recent Deliveries by checking the Response for 200, which means the Github event(commit) has been processed successfully.
Verify GitHub event (commit) is successful
Check the Response code is 200
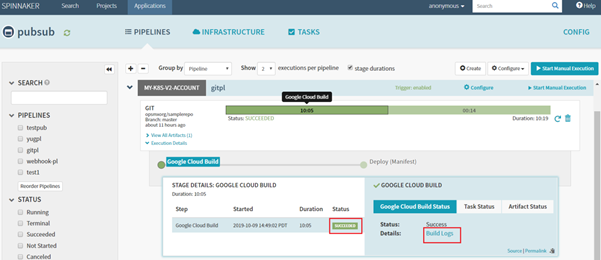
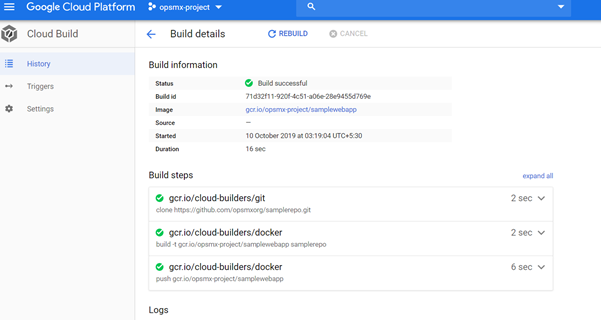
2. Ensure the Google Cloud Build stage is executed successfully as shown below:
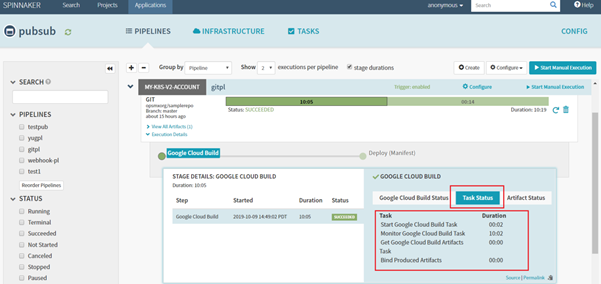
Click on the Google Cloud Build stage and check the status for SUCCESS. And click on Build Logs for checking logs on Google Cloud Build.Check Spinnaker Pipeline details for the successful execution of the Google Cloud Build stage
Check if the Google Cloud Build is a success
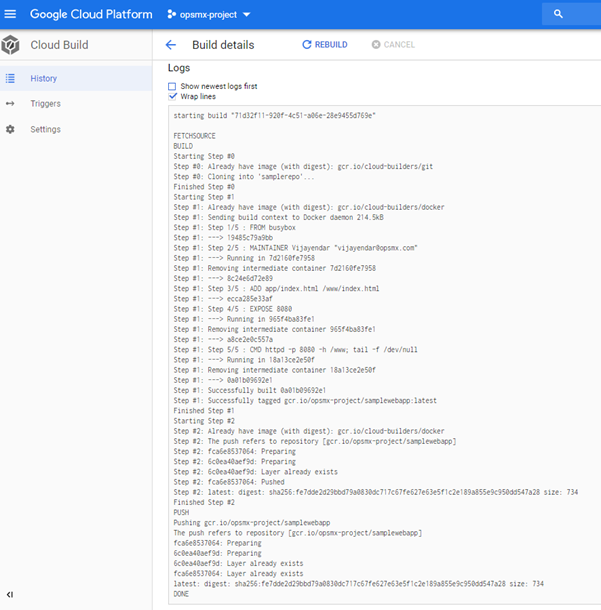
Check the logs for Google Cloud Build..
And click on Tasks Status for checking the status of tasks of Google Cloud Build.Check the status of tasks of Google Cloud Build
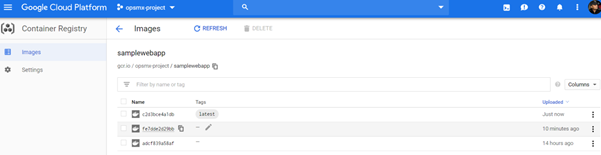
And ensure the resultant build is available in GCR as shown below:Check the Google Cloud Build is available in GCR
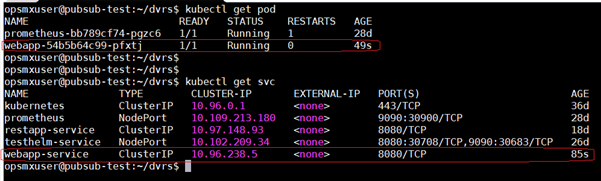
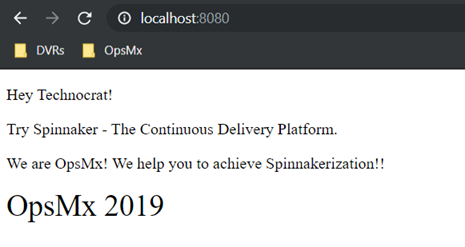
3. And see the subsequent deployment result in Kubernetes cluster as below:View the deployment results in the Kubernetes cluster
4. Check the sample web app result in the browser:Check the sample web app deployed by Spinnaker running in a browser
- VerificationMake a change into the repository, ex: https://github.com/opsmxorg/samplerepo.git for specified Filepath (example: sample.yaml) and ensure Spinnaker’s pipeline is auto-triggered. This can also be verified under Manage Webhook -> Recent Deliveries by checking the Response for 200, which means the Github event(commit) has been processed successfully.
-
OpsMx is a leading provider of Continuous Delivery solutions that help enterprises safely deliver software at scale and without any human intervention. We help engineering teams take the risk and manual effort out of releasing innovations at the speed of modern business. For additional information, contact us.
About OpsMx
Founded with the vision of “delivering software without human intervention,” OpsMx enables customers to transform and automate their software delivery processes. OpsMx builds on open-source Spinnaker and Argo with services and software that helps DevOps teams SHIP BETTER SOFTWARE FASTER.

0 Comments