The Ops team or the Platform engineering team implementing GitOps using ArgoCD will, at some point, need Single Sign On(SSO) for stronger user authentication. Argo CD is flexible in implementing any security IAM standard used in your enterprise. Argo CD supports a range of OpenID Connect (OIDC) providers such as Okta, Google SSO, Auth0, Linkedin SSO, etc., along with SAML and LDAP support for SSO configuration. Based on the type of authentication provider, one can update the configmap of Argo CD to get started with SSO. We have earlier covered ArgoCD and LDAP integration at length, and in this article, we shall discuss how to configure SSO in Argo CD by integrating with Okta.
Steps to integrate Okta and Argo CD
Create Argo application in Okta account
1. Create okta account if you don’t have
https://developer.okta.com/login/
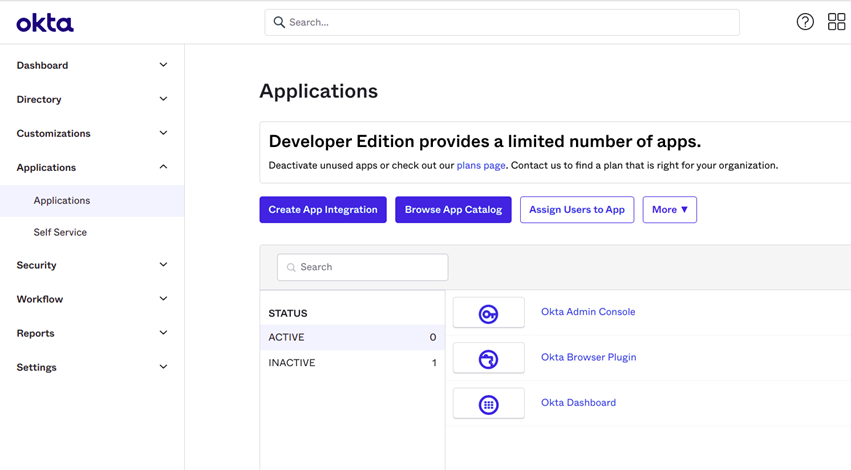
2. Sign in to the Admin Okta account and go to Application menu as per the image below:
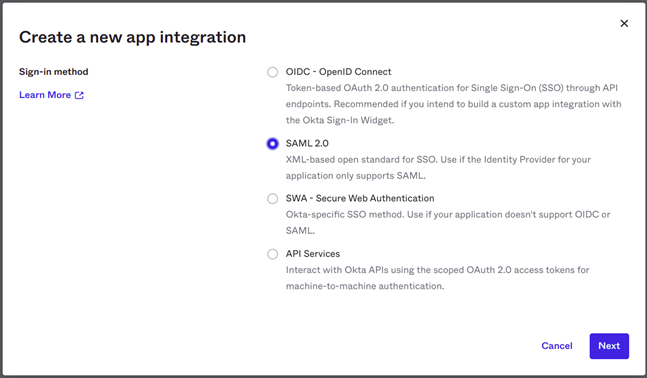
3. Click on Create App Integration to create a new integration and select SAML 2.0
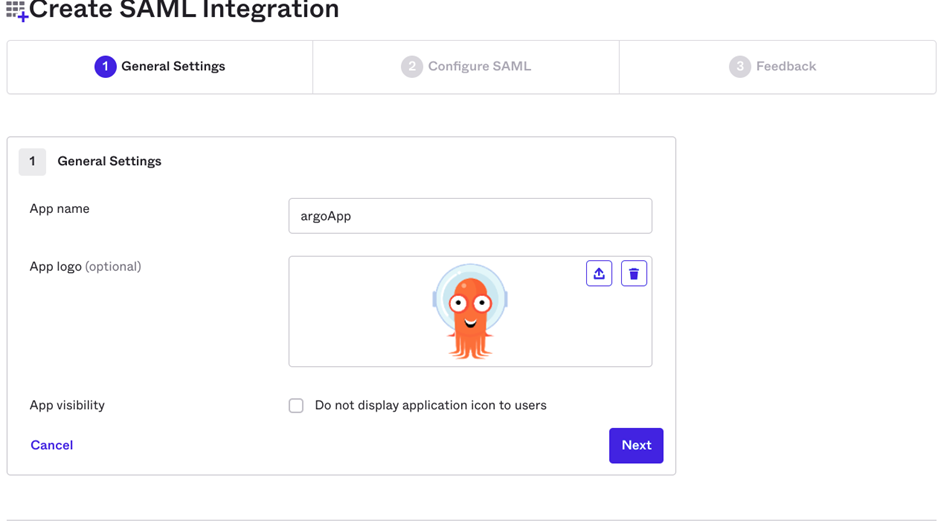
4. In the General Settings section, fill in the information about the application for which you are creating the SAML integration. I have used argoApp as the name.
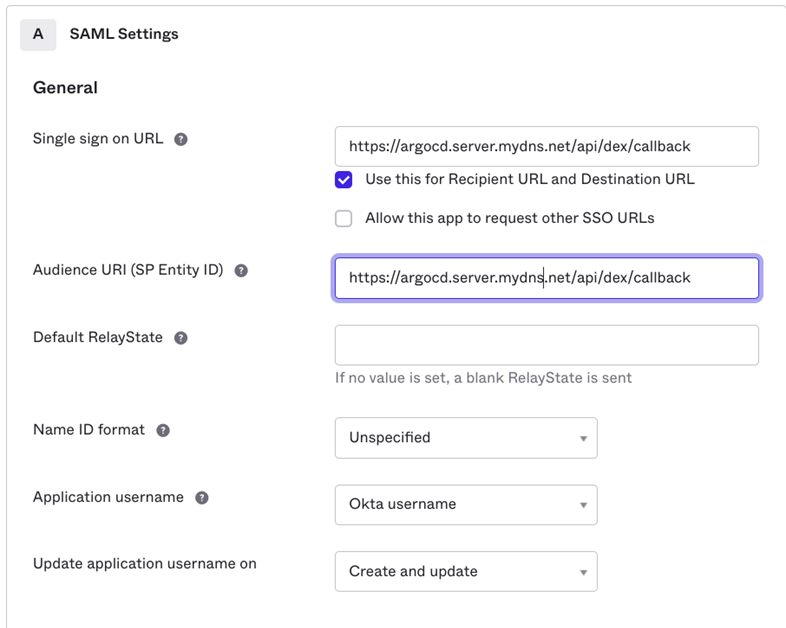
5. In the next section SAML Settings, provide SSO (single sign on URL) and Audience URI like https://<ARGOCD-SERVER-URL>/api/dex/callback
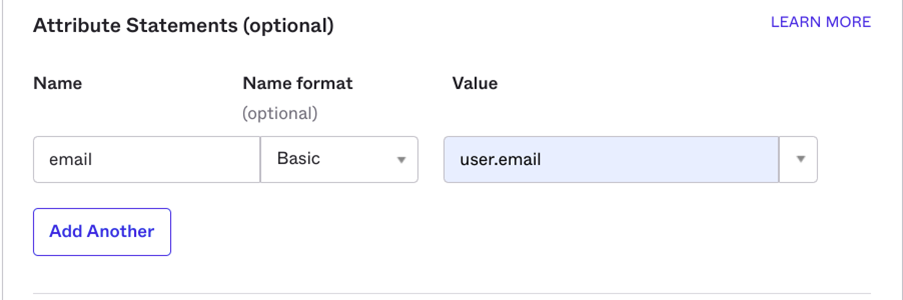
6. In the Attribute Statements section, provide attributes as email so that users can login using basic email addresses
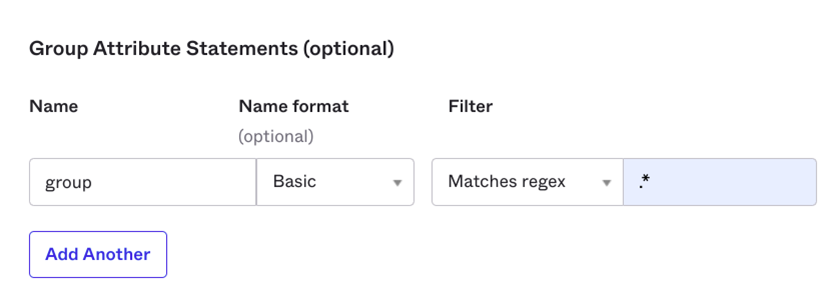
7. You can also add group information in the Group Attribute Statements section. This is for group attribute it can be all or to the specific groups
Filter:- .* pattern is for all groups
groupA|groupB|groupC pattern is for specific groups
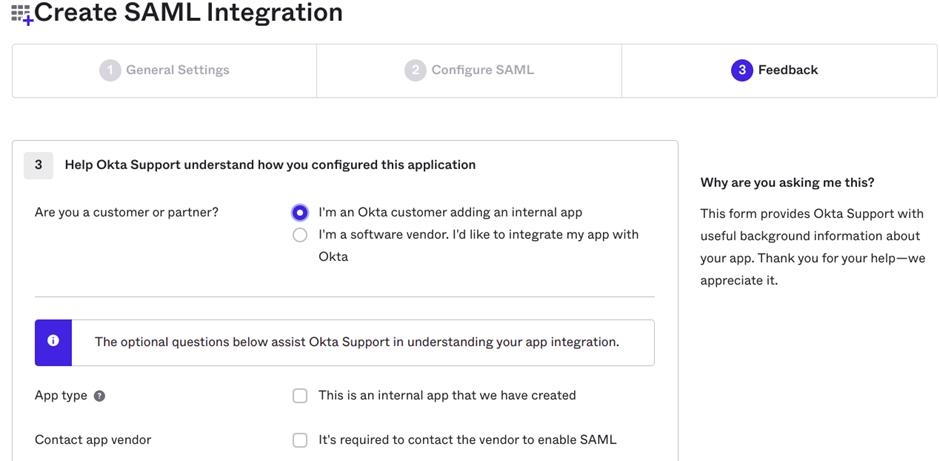
8. Click on Next then select I’m an Okta customer adding an internal app and Click on Finish.
9. Your app will be created.
Generate the SSO Url and X.509 certificates in Okta
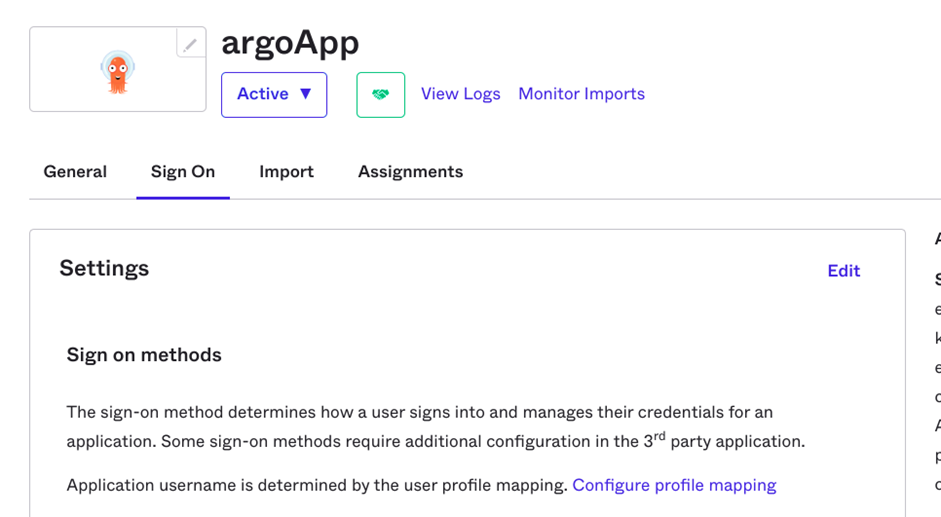
1. Once your app is created in Okta, you can go to the app details and click on Sign On
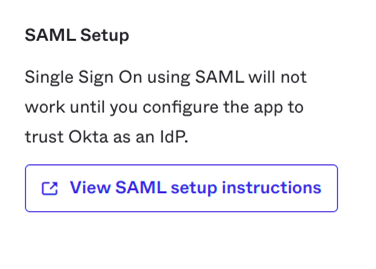
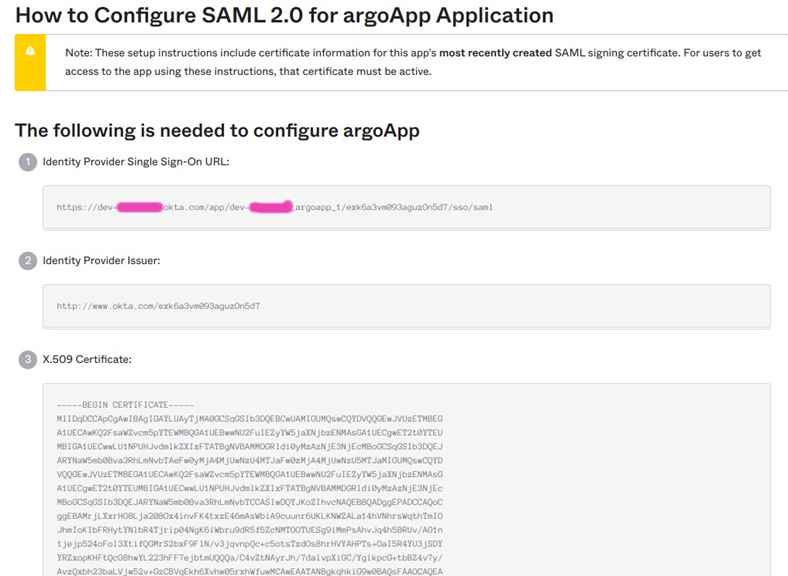
2. In the same window you will find View SAML setup instructions, click on it to download SSO Url and generate X.509 certificates.
3. Encode the ca file using command line (ignore if you have done encoding the certificate)
# base64 okta.cert -w 0
4. Make sure you have provided access to people and groups to Argo CD Application through Okta.
Make changes to configmap of argocd server
1. Go to cluster where Argo CD is deployed and edit the configmap called argocd-cm
- Encode the certificate to base64 in the point 3 and past it in the caData filed in the configmap
- Specify the sso and redirect url
- Specify the argocd url
apiVersion: v1
data:
url: https://argocd.server.mydns.net
dex.config: |-
connectors:
- type: saml
name: okta
id: okta
config:
ssoURL: https://dev-XXXXXX.okta.com/app/dev-XXXXXX_argoapp_1/exk6a3vm093aguzOn5d7/sso/saml
redirectURI: https://dev-XXXXXX.okta.com/app/dev-XXXXXX_argoapp_1/exk6a3vm093aguzOn5d7/sso/saml
usernameAttr: email
emailAttr: email
groupsAttr: group
caData: "LS0tLS1CRUdXXXXXXXXXXXXXXXX"
2. Save the configmap configuration, and the changes will get reflected. Once you login to Argo UI, you will see that the SSO has been implemented.
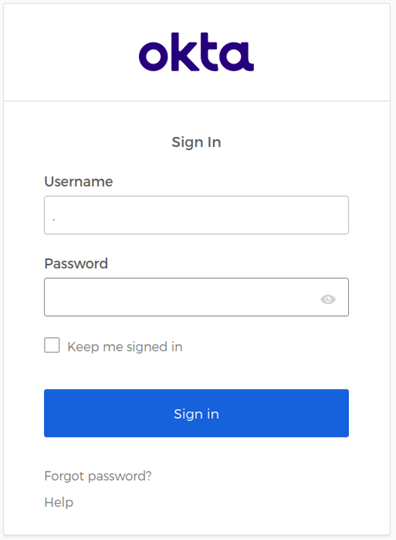
Access Argo UI with Okta sign on
Access the UI with the URL, UI looks as below, CLICK on LOG IN VIA OKTA. It will get redirected to the Okta login.
On successful login will be redirected to the ArgoUI.
Next Step
If you have an OIDC provider for which Argo CD does not provide out-of-the-box interoperability, then you can use Dex connectors to build the integration.
To save time and focus, you can try OpsMx Intelligent Software Delivery (ISD) for Argo (a SaaS version of Argo), which provides integrations to almost any identity provider and helps you get started with the GitOps initiative quickly.
Try ISD for Argo for free today.
OpsMx also provides Argo Center of Excellence (COE) for enterprises needing expert services or consultation on Argo CD and Argo Rollout implementation to expedite their GitOps journey.
About OpsMx
Founded with the vision of “delivering software without human intervention,” OpsMx enables customers to transform and automate their software delivery processes. OpsMx builds on open-source Spinnaker and Argo with services and software that helps DevOps teams SHIP BETTER SOFTWARE FASTER.


0 Comments